Article • IT security
What keeps a hospital’s immune system healthy?
‘You can’t get 100 percent security, you can’t avoid all risks – but you can improve security tremendously just by considering some rules,’ explains Torbjörn Kronander, Board member, CEO and President of Sectra AB.
Report: Marcel Rasch
Note: This interview was made earlier this spring before the ransomware attacks occurred mid-May.
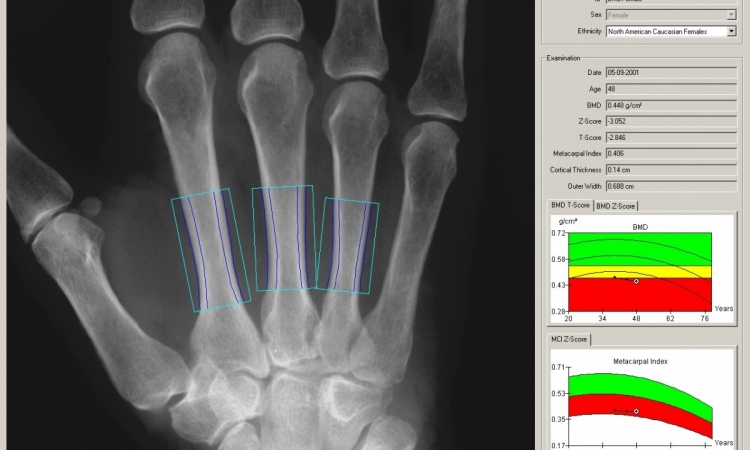
When hundreds, or even thousands, of machines and computers are connected with each other and diverse operating systems coexist with the PACS, hospitals have real IT security problems.
In addition, today all imaging equipment is no longer simple machines; devices are complex computers that could become infected by a virus. The problems hospitals face and what options they have to address those challenges were discussed by European Hospital and Dr Stefan Bücken, IT safety advisor in the Medical Centre for Information and Communication Technology at Erlangen University.
IT security can be easy

Ideally, a secure system would be totally isolated and blocked but, because there has to be an internet and data has to be exchanged, this situation is unthinkable. ‘We should see IT-security not as a curse, but compare it to our immune system,’ suggests IT-expert Torbjörn Kronander. ‘When we are born, we don’t know which germs and viruses will attack us in our lives, but the immune system has a mechanism to detect infections and take care of them. This is actually what a good IT-security system does; it monitors the environment, detects infections or potential harm and applies a mechanism to get rid of those.’
Unfortunately, most hospitals still handle their IT-systems incorrectly. They connect every workstation and every computer not caring enough about potential risks. ‘Hospitals must understand the seriousness of this situation and that they need to invest some time on re-organising their systems. Practically speaking, in PACS workstations, for example, never open private stuff, webpages, email and documents with attachments. Attachments can always contain contagious active elements,’ Kronander points out. Although zip-files carry the biggest risk because antivirus-software often cannot detect potential harm in them, Word-documents, Excel-sheets and even pdfs can also be contagious. ‘If you really want to stay safe, open and save documents only in a plain-text format like .rtf,’ he advises. ‘Never click “yes” to enable an active element in an attachment of a document.’
‘When a hospital looks for an IT-consultant, the management should ensure somehow that this consultant evaluates the entire system, considering all potential risks. He will also tell you that no user should have administration rights on their computers. There must be some kind of user identification and authorisation to access a workstation or a computer. There always must be log-in and log-out,’ Kronander points out. What sounds familiar to people who have paid attention at least to some IT-security subjects, appears to be totally new to other hospital staff members. ‘You won’t believe what we sometimes experience,’ the IT-consultant reveals, ‘In some hospitals, kids are coming to work with their parents and start playing computer games to dawdle. You never know what potential harm is on that system thereafter.’
According to Kronander ‘the most common security risk today are either USB sticks which inject a code into the system (a safe computer should have all USB ports glued by epoxy) or Phishing attacks, where users are fooled by a seemlingly correct email, often appearing to come from their boss or equivalent safe sender, into clicking on webpages with malicious content that injects malware into their system. Carefully setting up a system helps to prevent infections. ‘A lot of hospitals re-install their operating systems every single night to prevent potential harm on their computers. This means that documents in general cannot be saved locally. By having a completely new systems set-up every night, these hospitals avoid any risk of potential viruses that have been saved locally on a local computer during a working day.’
Medical technology comes with deeper risks
These attacks are no longer the work of a 14-year-old hacker somewhere
Torbjörn Kronander
The biggest challenge, however, is medical devices such as MR and CT, because these are not simple machines anymore; they are complex computers. ‘The problem here is that to receive FDA approval, the industry has to nearly freeze the version of the operating system they use. While Microsoft releases an upgrade for Windows every week, to take care of new threats, the version of a MR or CT system cannot be upgraded regularly enough without violating FDA regulations at the same time,’ Kronander explains. ‘This is a big problem the industry must take care about and for which we don’t have an appropriate solution up to today.
‘It must also be made known that hospitals are prime targets for “Ransom ware” where the hard disks of all available computers are encrypted and the key for decryption is only made available after a very sizeable amount of money has been paid to some account somewhere. In normal companies the reaction most often is to get a backup and knowingly lose a week of work or so. However, in hospitals, if the wrong medical devices are infected patients may even die. Therefore several hospitals have paid, and this has lead to even more attacks. It should also be noted that these attacks are no longer the work of a 14-year-old hacker somewhere. They are made by organised crime, the IT mafia.’
Profile:
With a doctorate in technology and Masters in Business Administration, Torbjörn Kronander PhD was the founder of the medical area, became an executive vice president of Sectra AB, and President of the company’s Medical Systems business section, accounting for 88% of Sectra’s sales. In 2012 he was appointed the company’s CEO and President. Today he is the largest shareholder of the Company.
This is the first part of a 2-part article. Read part 2 here.
16.05.2017