Article • Hospital technology
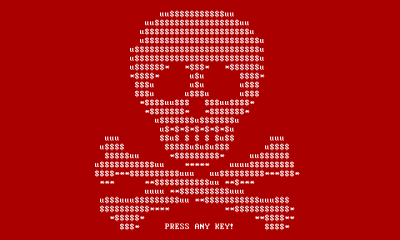
IT security: The user perspective
‘From an IT perspective, medicine is now networked to a very large degree, no matter which departments you look at,’ says Stefan Bücken, IT Security Officer at Erlangen University Hospital, Germany.
Report: Marcel Rasch

This is part 2 of a two-part article. Read Part 1 here.
Just a few years ago it was still possible to look at individual medical technology systems in isolation, but this is no longer possible. Medical technology systems must exchange data to make diagnoses and results available for patients’ medical care,’ he emphasizes.
‘From an IT department perspective, a hospital should be treated just like any normal company. We face the same technical problems with regards to systems networking as the automotive and other industries face. However, we do need to take into account the extended risks of medical treatments. And technical concepts for the comprehensive operation of networked systems in medical technology are still in their infancy.”
The expert sees one current problem in the increasing utilisation of cloud solutions. ‘Making these solutions completely secure is the great challenge we currently face.’ Bücken also believes that the so-called ‘Medical Device Isolation Architecture’ to safeguard networked medical technology is not future proof. ‘If you look at developments over the last few years, we no longer look at defined areas of IT. We can no longer run individual departments, such as radiology, with a designated MRI scanner and defined interfaces, but are moving increasingly in the direction of the utilisation of networked service structures, which go beyond individual systems limitations. ‘Apart from the utilisation of cloud services, there is also the large area of systems part of the Internet of Things (IoT), which constitute a particular challenge. Data protection and data security issues here are also similar, no matter whether we are looking at networked infusion pumps or the evaluation of diagnostic data somewhere in the cloud.’
The need for discussion
How safe can we make hospitals? Complete screening blocks medical advances, but an open-door policy is no solution either, Bücken says. Any disruptions to the running of a hospital can quickly result in life-threatening effects for patients. ‘We need to think very seriously about these structures in the near future,’ he emphasises. The publication of the IEC 80001-1 norm a few years ago was a first step in the direction of improved security for medical technology systems within networks. This norm describes risk management for the networked operation of medical devices. The German IT Security Law, the EU-Cyber-Security Guideline (NIS Guideline) and the EU Data Protection Law, which will be legally binding from 2018, will lead to a wider discussion around the increasing networking of IT in the healthcare sector. ‘However’, says Bücken, ‘management systems focused on organisation are only part of the solution, as paper is often very persistent.
‘We also require coherent basic technology concepts that need to be consistently applied. Although there are already some sustainable technical safeguarding procedures, all suppliers of medical technology systems are more or less working according to their own rules. In hospitals, however, these concepts must be amalgamated into a meaningful whole. It remains to be seen whether the current, diversified solutions will pass the test of time.’
A rift between users and manufacturers
So much for the users’ perspective – ‘the manufacturers’ perspective looks very different,’ Bücken points out. ‘The development and distribution of medical devices is particularly regimented. Manufacturers must abide by a comprehensive set of norms, utilise risk management procedures and undergo licensing procedures. Each change to a system requires companies to carry out repeated, comprehensive control and validation processes. In the context of the innovative environment of medical technology and the background of forever changing IT threats, this is an approach unlikely to last in the medium term,’ he explains.
Specifically, the orientation towards international markets often makes it difficult for manufacturers because each country has its own licensing procedure. ‘It’s understandable that manufacturers, once they have finally had their products approved, ideally don’t want to implement any changes. If they were to do so, this might entail having to go through the entire licensing procedure again,’ he points out. ‘On the other hand, however, the lack of regular software updates is dangerous from an IT security point of view. A hospital network will continue to develop gaps in security that need to be adequately filled. We are currently discussing these problems with medical technology specialists because medical device manufacturers continue to use Windows XP, which, as everyone knows, Microsoft officially stopped supporting in April 2014.
‘Therefore, manufacturers try to resolve the problem through risk management and read-only systems; but this hasn’t been thought out enough. Although the system returns to its original status after a restart it will be very vulnerable and easy to attack as long as it remains active around the clock, without any further security measures being implemented. Or, imagine a hospital where all systems run on Windows 10. Depending on the system version chosen, the hospital computers, based on Microsoft’s update strategy, would have to undergo operating system updates every six months. In a complex, heterogeneous IT environment, as found in hospitals, this cannot work. Manufacturers and users must engage in a much more intensive dialogue in the future.’
The liability issue remains unresolved
As is so often the case, the devil is in the details. ‘The issue of liability is very interesting. The hospital obviously has a duty of care. The Act on Medical Devices, however, states that manufacturers must take responsibility for their products and must clearly define how they can be used safely. But a hospital integrates such medical devices into a heterogeneous IT environment. Competing specifications issued by different manufacturers can quickly lead to mutually exclusive configuration requirements. Making the technology required for the provision of excellent medical care available to medical staff is a real challenge,’ Bücken confirms. One certainty exists. In this time of highly networked technologies, hospitals – with their inevitable constraints and security needs – will be unable to run alongside faster paced technological developments.
Profile:
Formerly head of the Systems Technology Department at Erlangen University Hospital for eight years, a role that included coordinating operational IT security, Dr Stefan Bücken became the hospital’s IT Security Officer in 2015. He is a qualified hospital manager and member of the UP KRITIS ‘Medical Care’ working group. Along with his medical IT skills Bücken also has a professional background in environmental and laboratory IT and in bioinformatics.
04.05.2017