Digital hygiene
Hospitals must be prepared for ransomware attacks
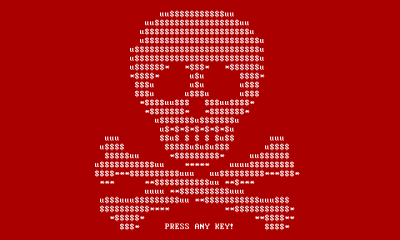
Dr Krishna Chinthapalli, a neurology registrar at the National Hospital for Neurology and Neurosurgery in London, describes how a virus - or “ransomware” - infected and locked computers at the Hollywood Presbyterian Medical Center in Los Angeles hospital in February 2016.

Rumours surfaced that the hospital was being held to ransom for $3.4m (£2.6m; €3.1m), though the hospital denied this. After 10 days the hospital paid a smaller ransom of about $17,000 to regain use of its computers. Hollywood Presbyterian was the first hospital to admit paying a ransom, writes Chinthapalli, but other US hospitals, in California, Indiana, Kentucky, Maryland, and Texas, were targeted in 2016. He points out that the number of ransomware attacks rose fourfold from 2015 to 2016, and so did the amount of money paid to hackers, to $1bn, according to the FBI. In the UK, a third of NHS trusts have reported a ransomware attack, he adds.
Chinthapalli argues that hospitals are ideal targets for ransomware companies. For instance, many use proprietary software that runs on ancient operating systems - and hold confidential patient information that can be sold to other criminals. As such, hospitals are probably more willing than other organisations to pay for quick recovery of their data.
So what can hospitals and their workers do, he asks? Digital hygiene - that is, keeping hardware and software as secure as possible - is essential, while frequent backups are also important. And when attacks do occur, the IT department must be informed quickly to isolate infected computers, he says. “We should be prepared: more hospitals will almost certainly be shut down by ransomware this year,” he concludes.
Source: The BMJ
15.05.2017